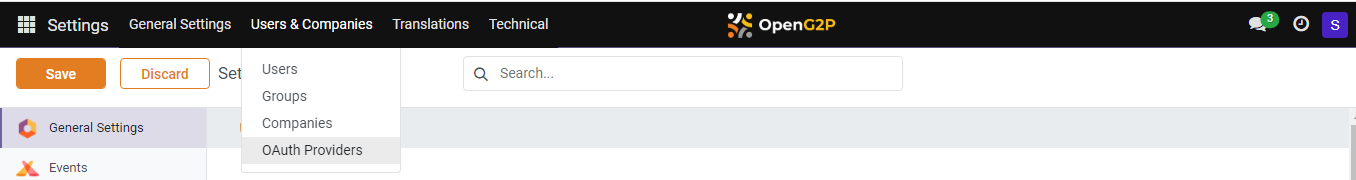
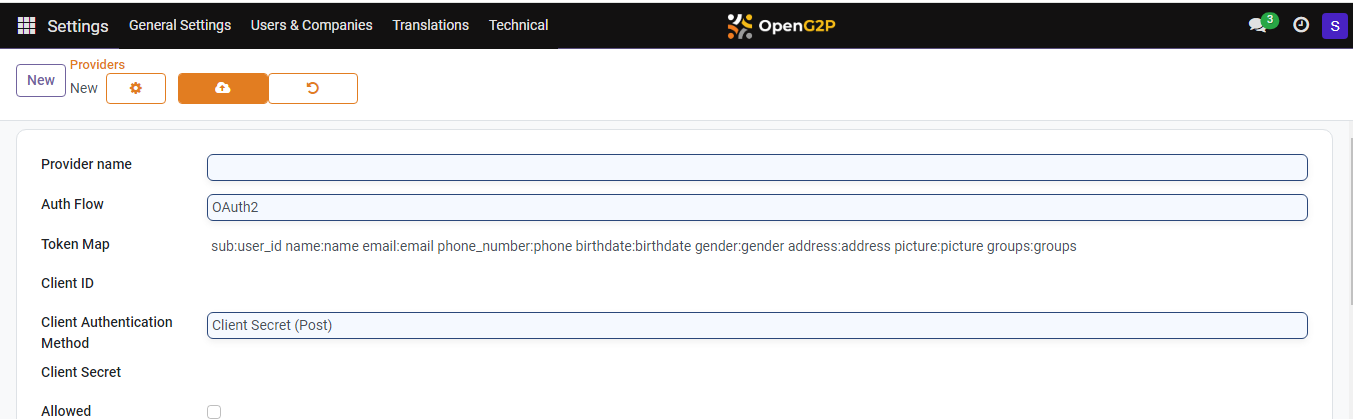
| Feature | Description | Value |
|---|---|---|
| Provider name | Enter the provider name. | For example: Keycloak for PBMS Login |
| Auth Flow | Select the option OpenID Connect Authorization Code Flow from the drop-down. | |
| Token Map | You can find a default value. In the default value change groups:groups to client_roles:groups . | |
| Client ID | The ID of the Keycloak client. To learn more refer to Keycloak Client Creation. | |
| Client Authentication Method | Select the option Client Secret (Post) from the drop-down. | |
| Client Secret | The Client Secret of the Keycloak client. To learn more, refer to Keycloak Client Creation. | |
| Allowed | Check the box to enable the option Allowed. | |
| Allowed in Self Service Portal | Uncheck the box. | |
| Allowed in Service Provider Portal | Uncheck the box. | |
| Login button label | Enter the label name for the Keycloak Login button. | For example: Note: This text with the button name will appear on login page. |
| Image Icon URL | Enter the URL of an image for the Keycloak Login button. | |
| Authorization URL, Userinfo URL, Token Endpoint, JWKS URL | These are to be configured as available in the well-known config of Keycloak. Note: Keycloak OIDC well-known configuration can be found in Keycloak Admin Console -> Realm Settings -> (Bottom of Page) Endpoints -> OIDC Endpoint Configuration) | |
| Verify Access Token Hash | Check the box to enable the option Verify Access Token. | |
| Allow Signup | Select the option Allows user signup from the drop-down. | |
| Signup Default Groups | Select the option User types/Portal from the drop-down. | |
| Sync User Groups | Select the option On every Login from the drop-down. |